Ryan McDonough


Beyond Outputs: Interpretability, Reasoning Posture, and Legal AI

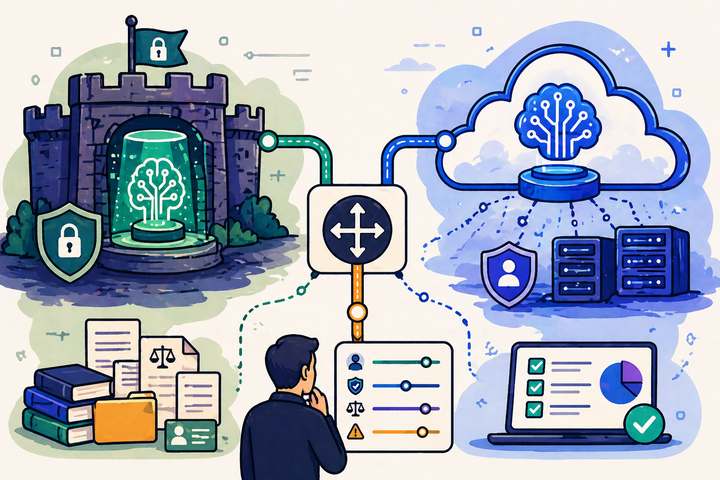
Behaviour ≠ output: the next phase of legal AI evaluation

Computer Use Agents Are A Bridge, Not The Architecture
Open source isn’t a playground: a practical guide for legal AI builders