Your Legal AI Stack May Now Sit on Foreign Critical Infrastructure
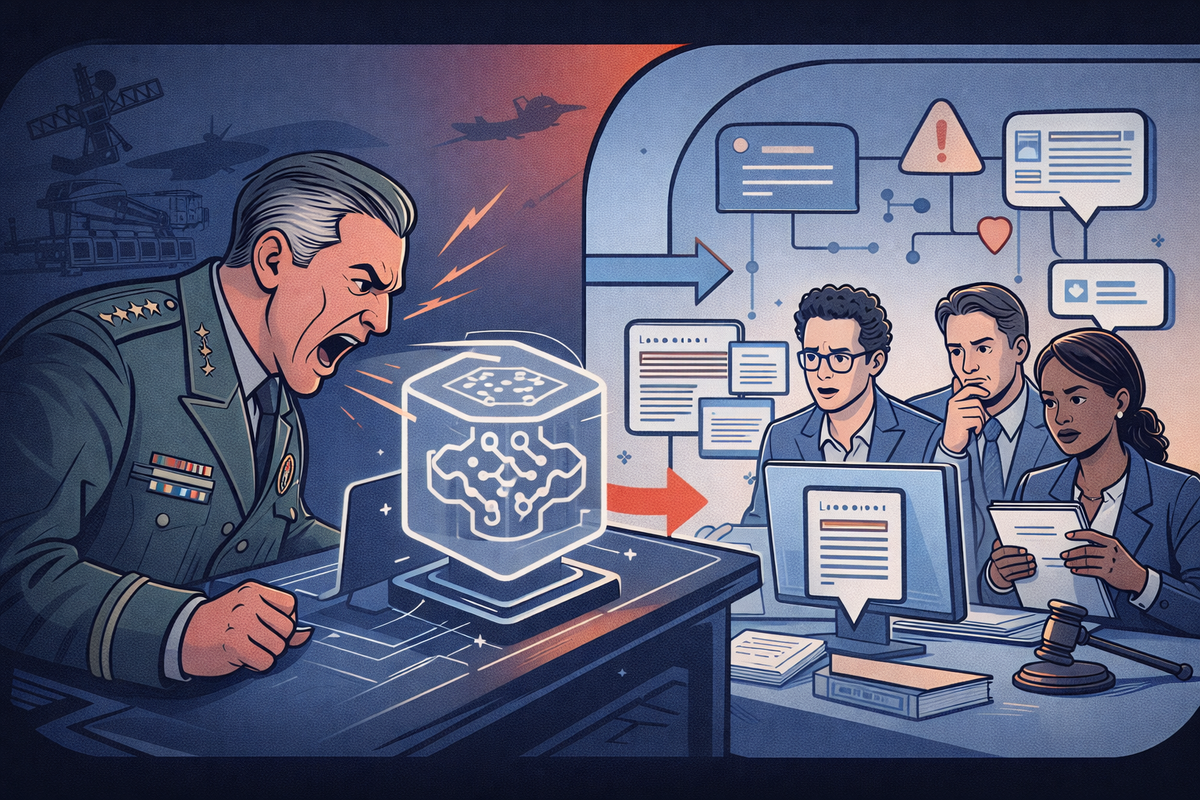
Over the past week there have been credible reports that the US Department of Defense (War) has asked Anthropic to expand how Claude can be used inside military environments, including relaxing some of the safeguards that currently prevent use in surveillance or autonomous weapons contexts.
There is also discussion of invoking the Defense Production Act if cooperation is not forthcoming.
Now even if none of that escalates further, something important has already been set in motion.
For the first time, access to a reasoning model is being discussed in the same breath as access to steel production or semiconductor fabrication, and if you are building legal technology on top of frontier models, infrastructure risk matters in ways most teams have not yet thought through.
This Is Not About Losing Access
The obvious reaction is to interpret this as an availability problem. People might immediately imagine a scenario where their contract review platform suddenly loses access to a frontier model during some future defence prioritisation event.
In practice, that is unlikely to be how this plays out, the more realistic downstream impact is behavioural rather than availability.
Frontier model providers already adjust refusal policies, update alignment layers, retrain safety filters and modify how concepts such as harm, risk or suspicion are interpreted. This happens regularly today in response to regulatory pressure or internal policy decisions, and most enterprise deployments never even notice.
Now imagine those same alignment layers being adjusted to satisfy national security deployment requirements.
Your sanctions exposure analysis, compliance monitoring or litigation likelihood modelling may still run perfectly well. Nothing crashes, nothing errors out, however the system simply begins to interpret borderline scenarios differently because the upstream reasoning engine has changed how it balances competing harms or operational permissibility.
For legal systems, that is often worse than an outage.
Interpretation Is the Real Dependency Surface
If finance loses compute capacity, it loses speed. If marketing loses compute capacity, it loses content.
If legal systems lose aligned reasoning, they lose classification boundaries, privilege assumptions, regulatory interpretation and escalation thresholds. The layer that tells the business what it is allowed to do becomes dependent on vendor alignment policy or upstream deployment commitments that sit entirely outside your procurement framework.
You have effectively imported an external regulatory philosophy into your internal compliance tooling without meaning to.
Nothing has gone offline... the answers are just slightly different now.
Why This Matters for Advice Defensibility and Consistency
This is where the issue moves beyond engineering.
Partners do not lose sleep over model alignment, they (should) lose sleep over whether advice can be defended if challenged later.
If a legal AI system contributes to:
- advice preparation
- matter triage
- risk classification
- sanctions interpretation
and the reasoning behaviour of that system changes between matter intake and regulator audit, you may now have two materially different interpretations of the same facts produced by the same workflow at different points in time.
Which raises questions most firms are not currently equipped to answer.
Which version informed the original advice?
Can we reconstruct the reasoning environment that existed at that time?
Was this advice produced under a different interpretive standard?
Most firms version documents, however very few are versioning the reasoning substrate that influenced those documents.
Legal Ops teams will recognise a related issue around consistency. If two similar contracts are assessed six months apart and one is escalated for review while the other is not, due to upstream behavioural drift rather than an internal policy change, that becomes operationally indistinguishable from inconsistent legal guidance.
Your firm may appear to have changed its legal position without intending to.
The Architectural Response
None of this means firms should avoid frontier models. They remain the most capable tools available for open ended clause interpretation or reasoning across multi document matters.
The more useful response is to understand which parts of your legal AI stack actually require frontier level reasoning, and which parts do not.
A surprising amount of legal workflow can already be handled by evaluated open weight models, domain tuned local deployments or deterministic retrieval pipelines. Clause extraction, obligation mapping, document classification and timeline construction are structurally bounded tasks. They are repeatable, benchmarkable and increasingly well suited to smaller models running on device, on prem or inside a controlled tenant with degradation curves you can actually observe.
Frontier models can then be retained for genuinely ambiguous interpretive tasks such as contextual balancing tests, novel clause risk analysis or cross jurisdictional regulatory reasoning.
In other words, the areas where ambiguity is the point.
Behavioural Drift Is Now a Runtime Risk
Most legal AI deployments evaluate models during vendor selection, during an initial proof of concept, and perhaps before a major release, from that point onward they assume behavioural stability.
That assumption made sense when the underlying system was some static rules engine or a versioned NLP model deployed inside your own tenant.
It makes far less sense when your compliance triage system ultimately depends on an external reasoning layer that may be periodically realigned or refusal tuned without a version number ever changing in your integration layer.
In most firms today, the first sign that a model has changed its reasoning behaviour will be an unexpected escalation, a missed clause classification or a contract risk score that no longer aligns with internal policy.
In other words, an outcome level discrepancy noticed by a lawyer after the fact, and that is governance by anecdote.
Continuous Legal Evals
Instead of asking whether a model performed well during onboarding, the more relevant question becomes whether it is still reasoning in line with your internal expectations right now.
Practically, this means maintaining a small but representative set of clause interpretation tasks, risk classification examples, sanctions exposure scenarios and jurisdictional edge cases that reflect how your firm actually defines acceptable outputs.
These are then run on a continual (say hourly) basis against the currently deployed reasoning layer.
If interpretation of a vague standard such as material risk or reasonable suspicion begins to deviate beyond a defined tolerance, that becomes a measurable governance signal rather than a subjective concern raised by a reviewer days later.
Designing for Rapid Substitution
Detection is only half of the story.
The more important architectural question is how quickly you can shift your AI stack if that deviation persists.
If your workflow assumes a direct dependency between a frontier API and your retrieval pipeline, any drift upstream affects every downstream task simultaneously.
If instead your architecture routes extraction, classification and baseline policy scoring through locally evaluated models before escalating genuinely ambiguous questions to a frontier model, you can temporarily disable interpretive escalation, route borderline tasks for human review or substitute an alternative reasoning model without shutting down the entire system.
Extraction, classification and timeline construction can continue locally while interpretive summarisation or risk balancing is escalated manually until evaluation results stabilise.
You gain the ability to pause interpretive automation without losing structural automation.
In practical terms, this changes legal AI assurance from pre deployment benchmarking to continuous behavioural monitoring with defined intervention thresholds.
Which starts to look much closer to how firms already manage financial model risk or credit scoring pipelines than how they currently manage legal automation tools.
This is not about preparing for geopolitical collapse (though who knows...), but it is about recognising that reasoning infrastructure may now sit closer to export controlled compute than to ordinary SaaS, and planning your architecture accordingly.